Denial of Service (DoS) attack refers to the attempt to prevent the availability of computer information or services to its intended users. An attacker is able to prevent you from accessing email, websites, online accounts (banking, etc) or any other services. In some cases, a DoS attack forces websites accessed by millions of people to cease operation and cost the targeted person or company time and money. The most common way to perform a DoS attack is when an attacker “floods” a network or server with as many request and data as possible.
When you access a particular website through your browser, you are sending a request to the website’s server to transmit data to your computer. As the server can only process a limited number of requests at a time, your request will not be processed in the event that an attacker sends a very large amount of requests to the server concurrently, beyond what the server can handle. This is known as DoS.
An attacker is also able to utilize spam email messages to perform a similar attack on your email account. Our corporate or personal email accounts are usually allocated with a fixed storage quota. If an attacker floods our email inbox with many spam email messages or email messages with huge attachments, our available storage space would be used up and we would be denied from receiving legitimate messages.

Distributed Denial of Service (DDoS) attack on the other hand, is launched by an attacker through the use of an army of computers to attack the victim computer or server, to deny them in providing resources or services to its intended users. The attack is “distributed” because it utilises multiple computers, including yours, to perform the denial of service. To perform a DDoS attack, the tactic of botnet or a collection of inter-connected computers is most often used.
Botnets or zombies are computers that are remotely controlled by an attacker stealthily, as their security defenses have been breached. Computers that do not have the appropriate security measures such as anti-virus software or firewall in place are common victims of botnet. The attacker is able to control your computer in sending huge amount of request and data to a particular website or email address once it is compromised.
DDoS is a popular attack method since numerous machines produce more attack traffic as compared to a single machine, and thousands of attacking machines are more difficult to trace and turn off. Identifying a DoS or DDoS attack is not easy as users often confuse attacks with usual technical problems with the network or systems maintenance delays.
Symptoms of Botnets/ Zombie Computers
The symptoms of computers that have been compromised to serve as a botnet or zombie in a DoS/DDoS attack are very similar to other malware infection. A user may detect if a computer is infected with malware by looking out for the following symptoms:
- Unusually slow network performance (opening files or accessing websites)
- Unavailability of a particular website
- Inability to access any website
- Dramatic increase in the number of spam emails sent and received
Recovering from an Attack
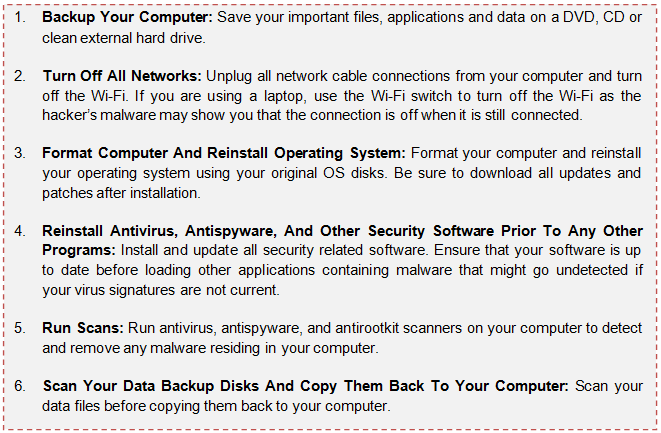
In the unfortunate event that your computer has been compromised and became a zombie or you suspect that you or your organization is targeted by a DoS/DDoS attack, apart from contacting SingCERT to report the incident and for further advice, you may use the following steps to recover from a DoS/DDoS attack:
Tips to mitigate a DoS or DDoS Attack
1 | Install and Maintain Antivirus Software | Installing an antivirus software and configure automatic update of the latest virus definitions helps to detect and remove the malware from your computer, thereby preventing it from becoming a zombie. |
2 | Install and Configure Network Protection | Firewall: Limit the type of traffic that can pass through and filter out unwanted content or suspicious traffic. |
3 | Follow Good Security Practices for Distributing Email Address and Apply Email Filters |
|