Advisory on Axios Supply Chain Attack via Compromised npm Account
1 April 2026
A critical software supply chain compromise has been identified affecting the widely used JavaScript HTTP client Axios. Organisations using affected versions of the product are advised to assess their systems and networks for potential compromise.
Background
A critical software supply chain compromise has been identified affecting the widely used JavaScript HTTP client Axios. Threat actors successfully compromised the npm account of a primary Axios maintainer and published unauthorised malicious package versions to the npm registry, resulting in a global supply chain attack affecting Axios users worldwide.
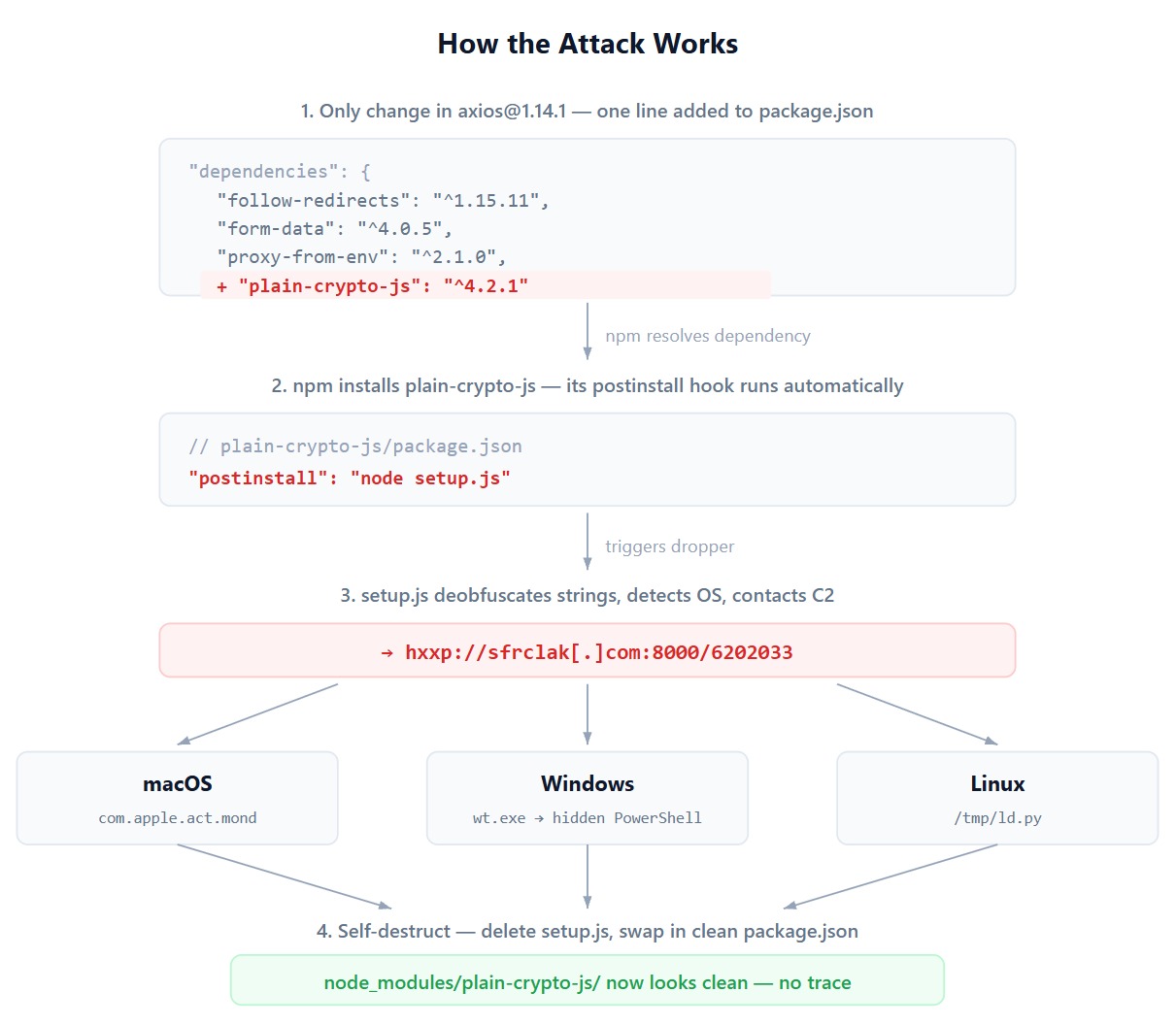
The affected releases contain a malicious dependency designed to execute a post-install payload, resulting in the deployment of a Remote Access Trojan (RAT) across multiple operating systems, including Windows, macOS, and Linux. The attack demonstrates a high level of sophistication, involving credential compromise, Continuous Integration and Continuous Deployment (CI/CD) pipeline bypass, dependency injection, and anti-forensics techniques.
Affected Product Versions:
axios@1.14.1
axios@0.30.4
Overview of the attack
Source: https://socket.dev/blog/axios-npm-package-compromised
Compromise of npm maintainer account credentials
Unauthorised publication of malicious package versions
Injection of a malicious dependency into production releases
Execution of malicious code during package installation via post-install scripts
Indicators of Compromise (IoCs)
Malicious npm Packages
axios@1.14.1 — shasum: 2553649f232204966871cea80a5d0d6adc700ca
axios@0.30.4 — shasum: d6f3f62fd3b9f5432f5782b62d8cfd5247d5ee71
plain-crypto-js@4.2.1 — shasum: 07d889e2dadce6f3910dcbc253317d28ca61c766
Network Indicators
C2 domain: sfrclak[.]com
C2 IP: 142[.]11[.]206[.]73
C2 URL: http[:]//sfrclak[.]com:8000/6202033
Unique POST body identifiers used by the malware for OS fingerprinting:
C2 POST body (macOS): packages.npm.org/product0
C2 POST body (Windows): packages.npm.org/product1
C2 POST body (Linux): packages.npm.org/product2
File System Indicators
macOS:
/Library/Caches/com[.]apple[.]act[.]mond
Windows:
Persistent:
%PROGRAMDATA%\wt.exe
system.bat (persistence script)
SHA256: f7d335205b8d7b20208fb3ef93ee6dc817905dc3ae0c10a0b164f4e7d07121cd
Temporary (self-deletes):
%TEMP%\6202033.vbs
%TEMP%\6202033.ps1
Linux:
/tmp/ld[.]py
Recommended Actions
Organisations are recommended to adopt the following measures to protect against supply chain attacks:
Remove and remediate affected versions:
Downgrade to safe versions: axios@1.14.0 or 0.30.3
Eliminate malicious artifacts: Remove plain-crypto-js from all environments and node_modules
Verify that no unauthorised files or scripts remain on affected systems
Assume potential compromise: rotate all credentials, including:
API keys
Access tokens
SSH keys
Environment secrets
Perform threat hunting and detection:
Scan systems for listed IoCs
Review CI/CD logs for:
Unexpected outbound network connections
Suspicious installation-time activity
References
